I’ve said it before and I’ll say it again. WordPress is very safe, until it isn’t.
Most of that is up to you.
Interestingly I saw a post the other day (and shared it to Facebook) about “How Attackers Gain Access to WordPress Sites“. It was written by a well known plugin company called WordFence. It got a little technical for the average user but the thing that stood out for me was this simple graphic.
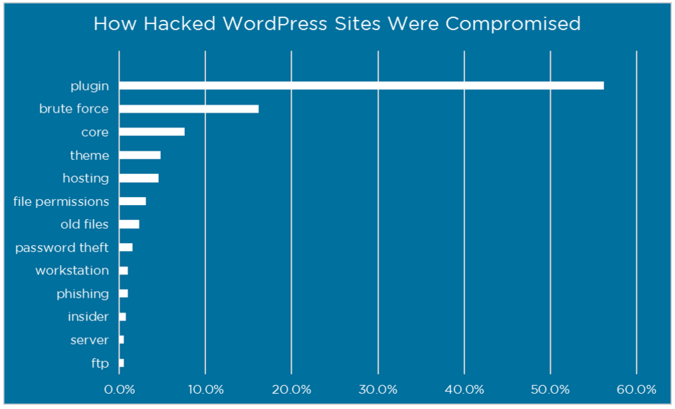
Plugins. It’s pretty scary sometimes when I look in the backend of sites and see a wrath of plugins just sitting there. I was hired to fix a site recently and they had over 50 plugins that past developers added over the years. I looked at each one, decided what was necessary and deleted the rest. It’s now down to 11 plugins that I know and trust.
I also had a client who added a plugin that essentially locked them out of their site. I had never heard of the plugin before and would have never added it to a site. They found it online somewhere, thought it sounded good, added it and then everything started crumbling down.
Plugins are little programs. They might do something that effects the look of your site, or the function, or a variety of other things. They are written by nice coders who saw a problem, wrote some code to fix the problem and then offered that solution up to the masses. That’s usually a good thing.
There are also bad coders who, like all other bad guys, look for opportunities to take advantage of the unknowing. They write programs that seem to fix a problem but behind the scenes can do very malicious things. By you adding a plugin, you are essentially inviting them in to your home to do whatever they want.
Always add only plugins that are trusted – if not you, by the community. Right now there are over 40,000 plugins available in the WordPress Plugin Directory.
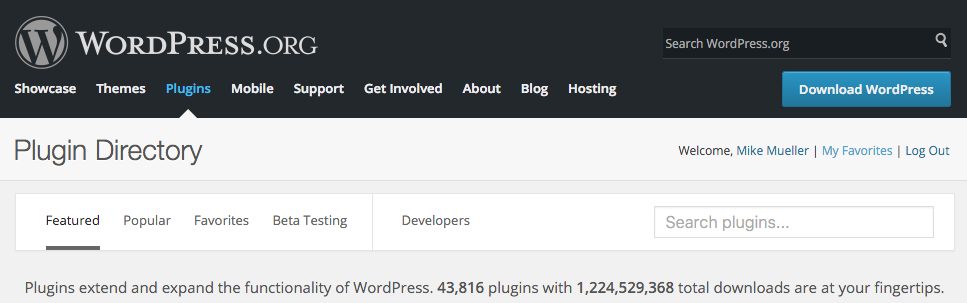
Each one in the Depository was written by a coder or team of coders. once they thought they had something good, they submitted it to be included. Before it showed up for the public to use a really smart person looked at the code and reviewed it, most likely it was Mika Epstein. If the code was approved it became public.
That doesn’t mean the code was perfect. As the hackers get better and new vulnerabilities are discovered the code needs to be patched. No fear, the good guys will patch their code and that plugin will issue an update. That’s when you see that little notification light up.
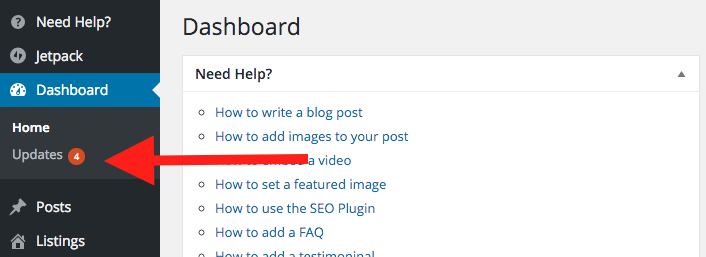
Failing to update the plugins might mean you are wide open to letting the bad guys in.
BUT WAIT! THERE’S MORE!
Sometimes plugins that were written properly to begin with get abandoned. When that happens the plugin might leave you as vulnerable because there was nobody to plug the security hole. Because there was no update, there was also no notification on your part.
There’s also another bad thing that can happen to plugins. The abandoned plugins might be taken over by bad guys who rewrite the code seemingly to update the plugin but also to allow them to get in and do their bad guy things. So what might start out as a good plugin might become a bad one down the road.
POPULAR DOESN’T MEAN SAFE
Just a little bit ago a very popular plugin that was commonly used in some themes had a huge security hole. You can read about it in, “Slider Revolution Plugin Critical Vulnerability Being Exploited“. I’ve never used those “themes” as they are not always the best built.
(I exclusively use the Genesis framework and child themes)
This is very different from just a few years ago when the leading opportunity was from your server.

CONCLUSION:
Always use plugins that you know you can trust. If you need help knowing what you can and what you cannot – just ask.
Always keep your site up to date. And always remember to backup your site before you update. Always!
UPDATE 4/7/16: You’ve heard about the so called Panama Papers Breach? Turns out that was a case of them NOT using updated plugins. Specifically, they were using an older version of the Rev Slider Plugin! That’s how the bad guys got in!
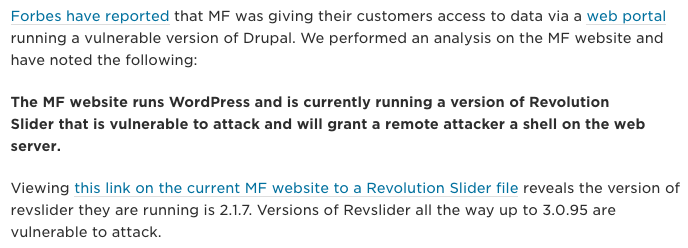
Source: https://www.wordfence.com/blog/2016/04/mossack-fonseca-breach-vulnerable-slider-revolution/
- The Ultimate Guide to Writing the Perfect Blog Post - March 14, 2023
- 8 Questions Your Web Developer Should Have Asked - April 27, 2021
- Slack, Chat or Discord? - April 6, 2021